Threat Actors disguise the Remcos RAT malware in PDF files

The Vcrums malware targets browsers and popular apps
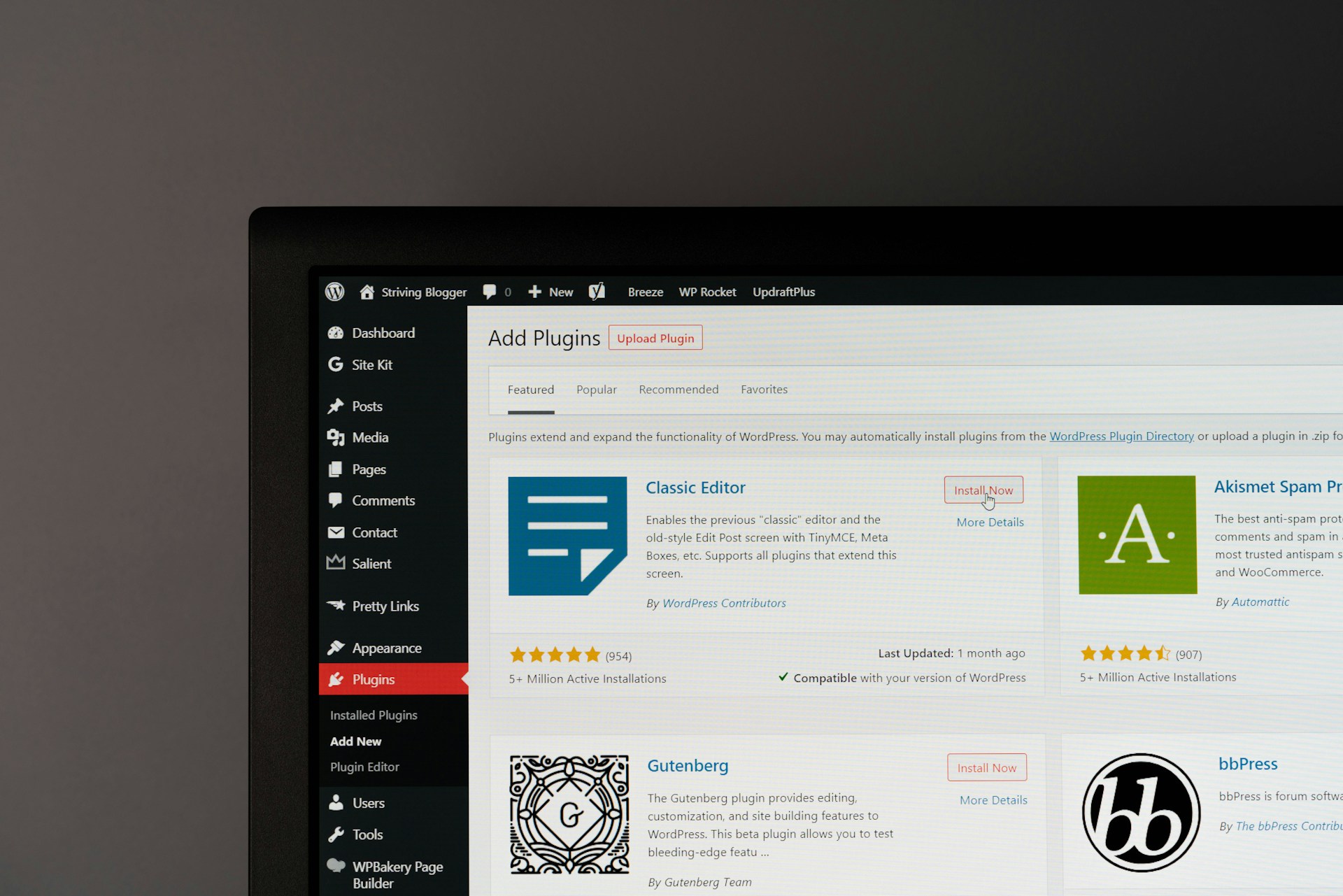
Thousands affected in the latest WordPress brute force attack, poses a challenge for cyber experts
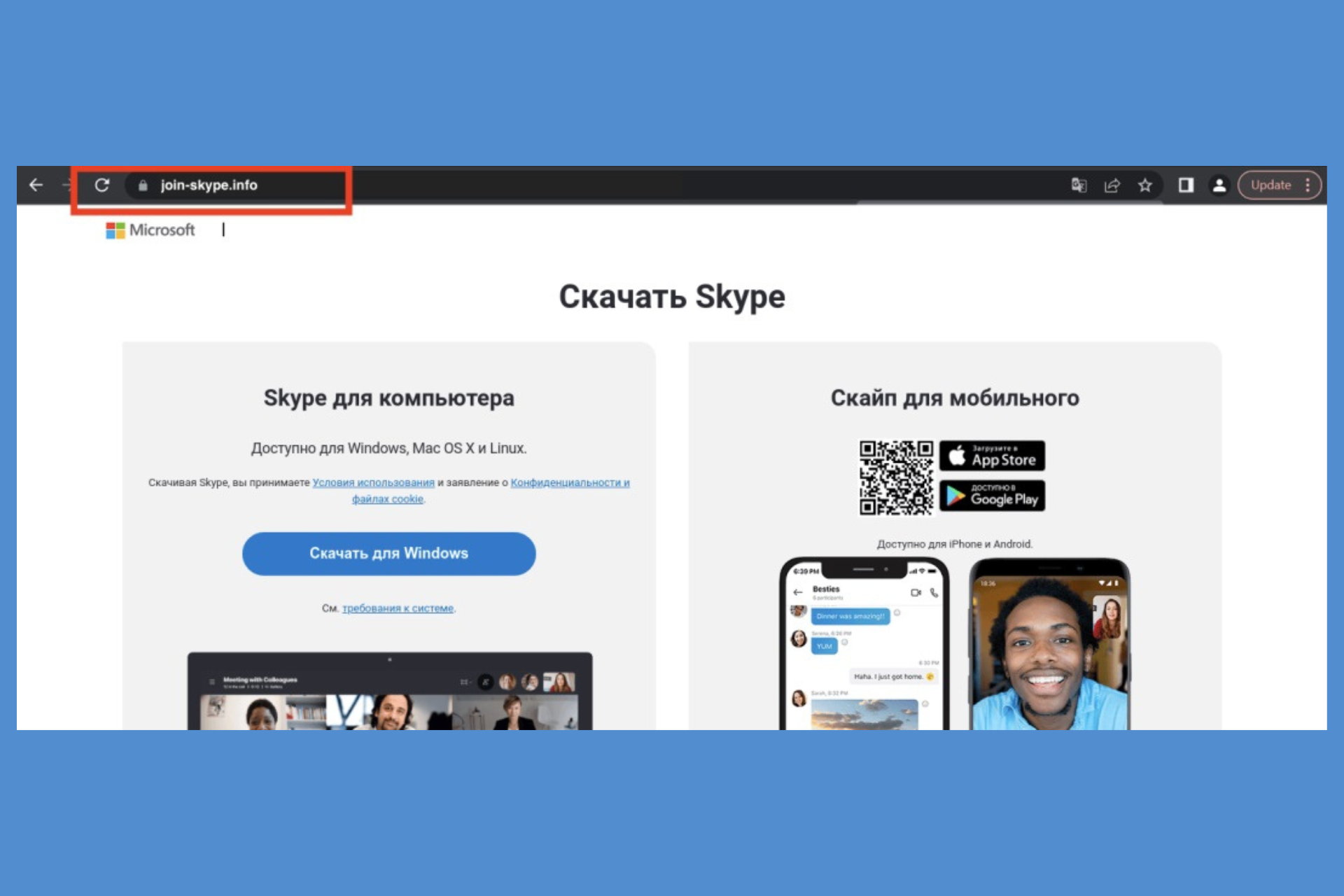
RAT malware is targeting Zoom, Skype and Google Meet users
Acemagic caught red-handed installing malware on its devices
The malware dropper TicTacToe is targeting Windows users

Facebook Ads spread the Ov3r_Stealer malware disguised as job offers
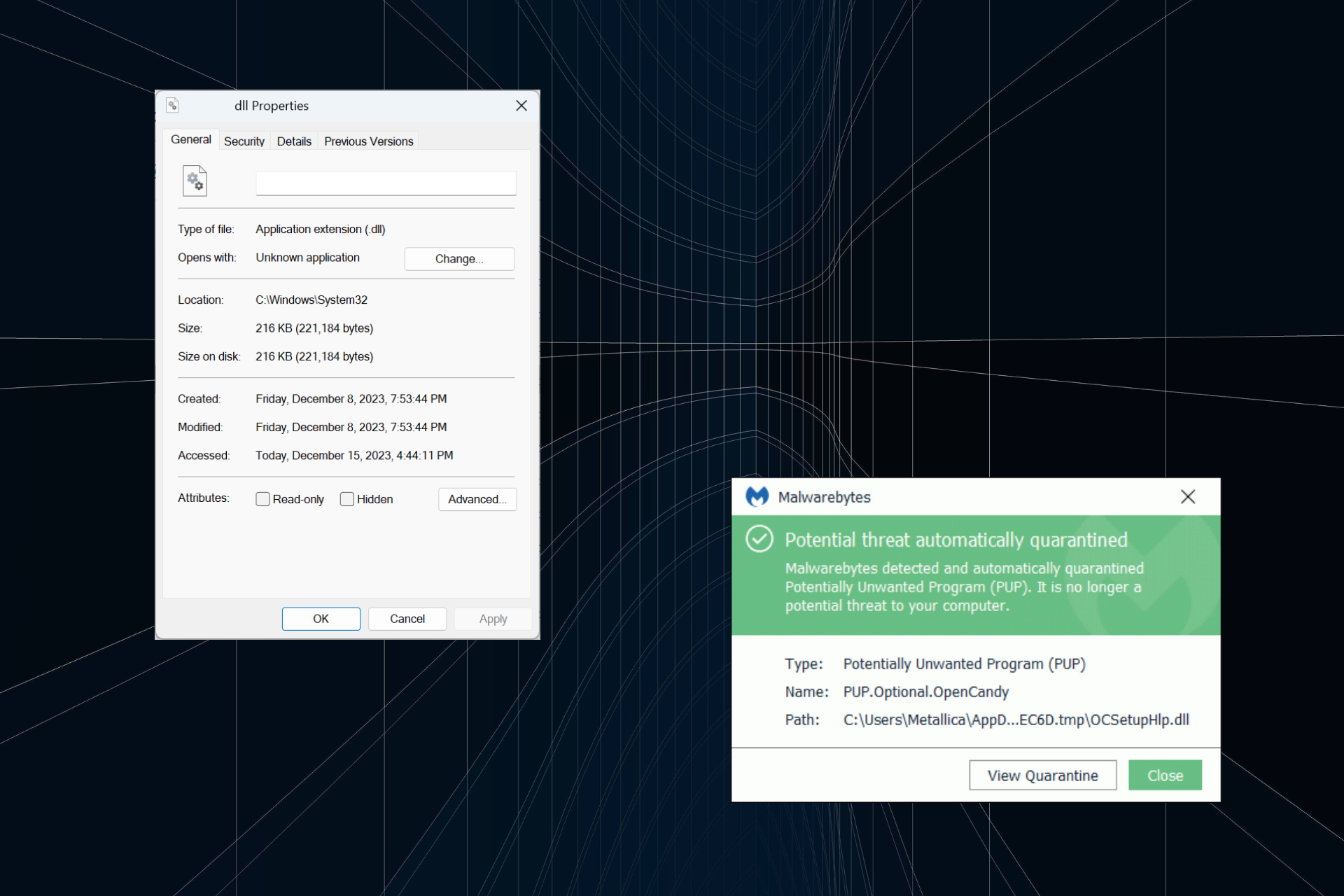
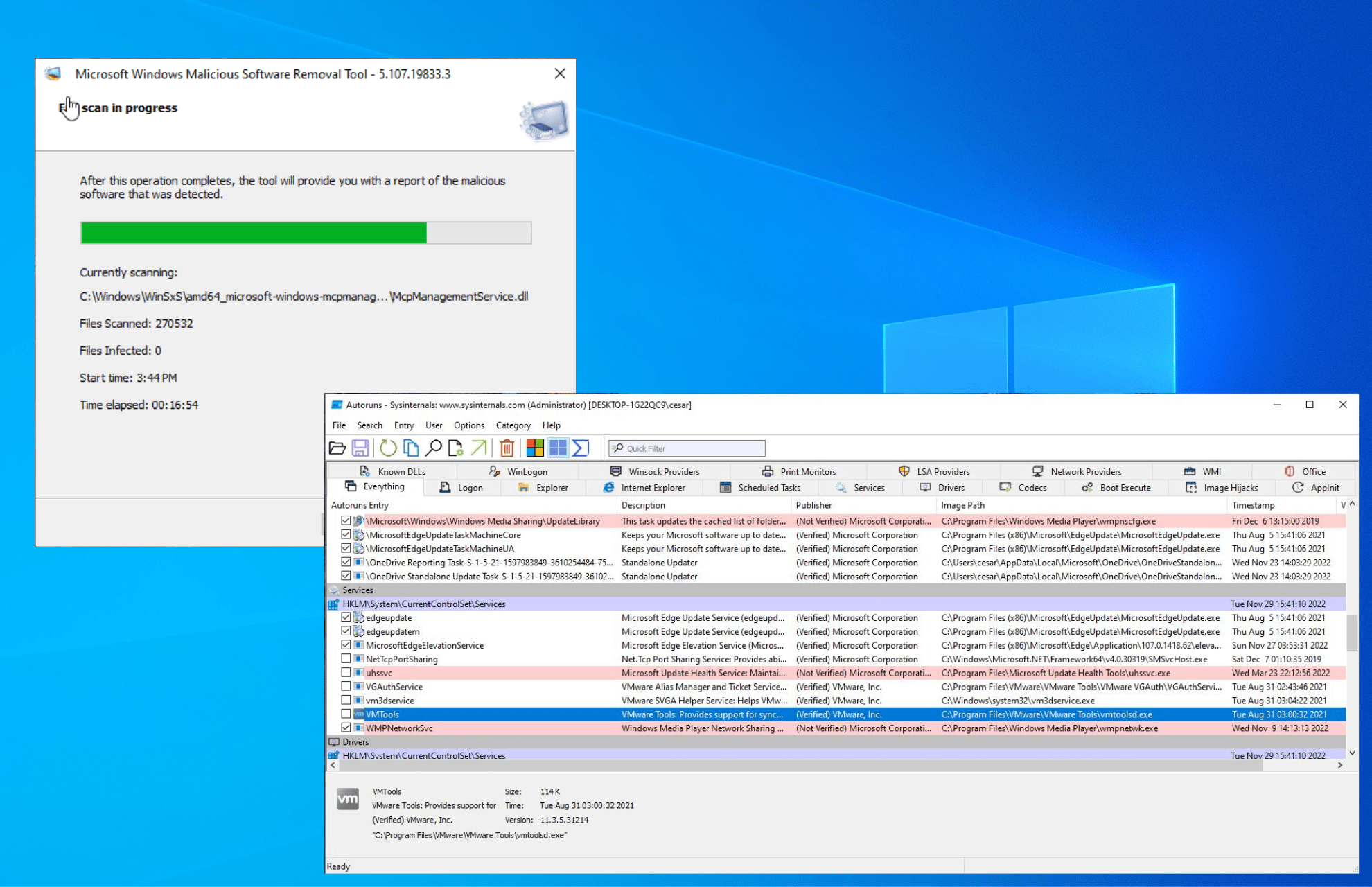
Is OCSetupHlp.dll a Malware and How to Remove it
Zeus Malware: What is & How to Prevent or Remove it
Can You be Hacked by a QR Code? [Prevention Guide]
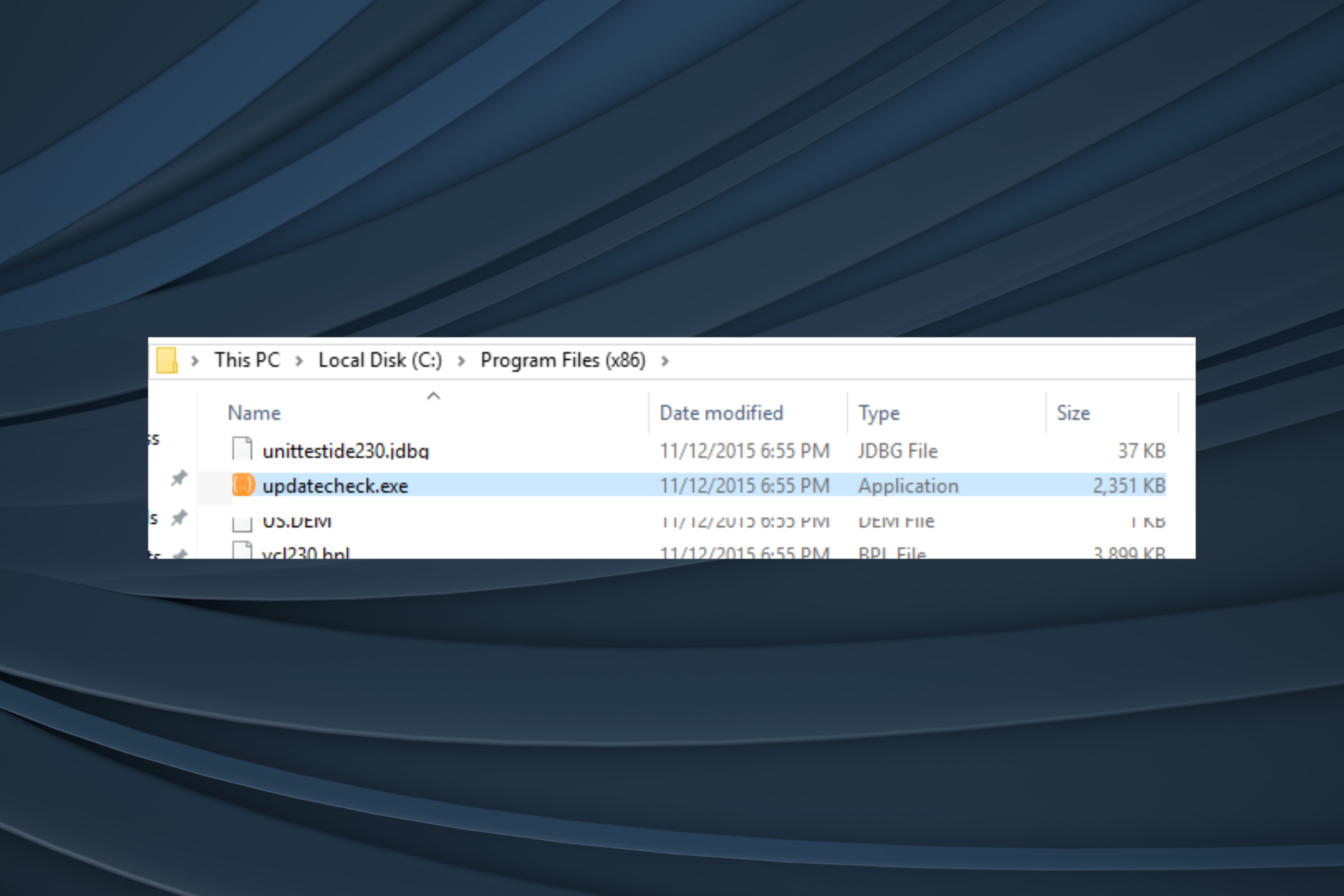
What is UpdateCheck.exe & What is it Used for?

Beware of these weather-named threat actors

This new CISA tool can prevent hacking attempts in Microsoft’s cloud
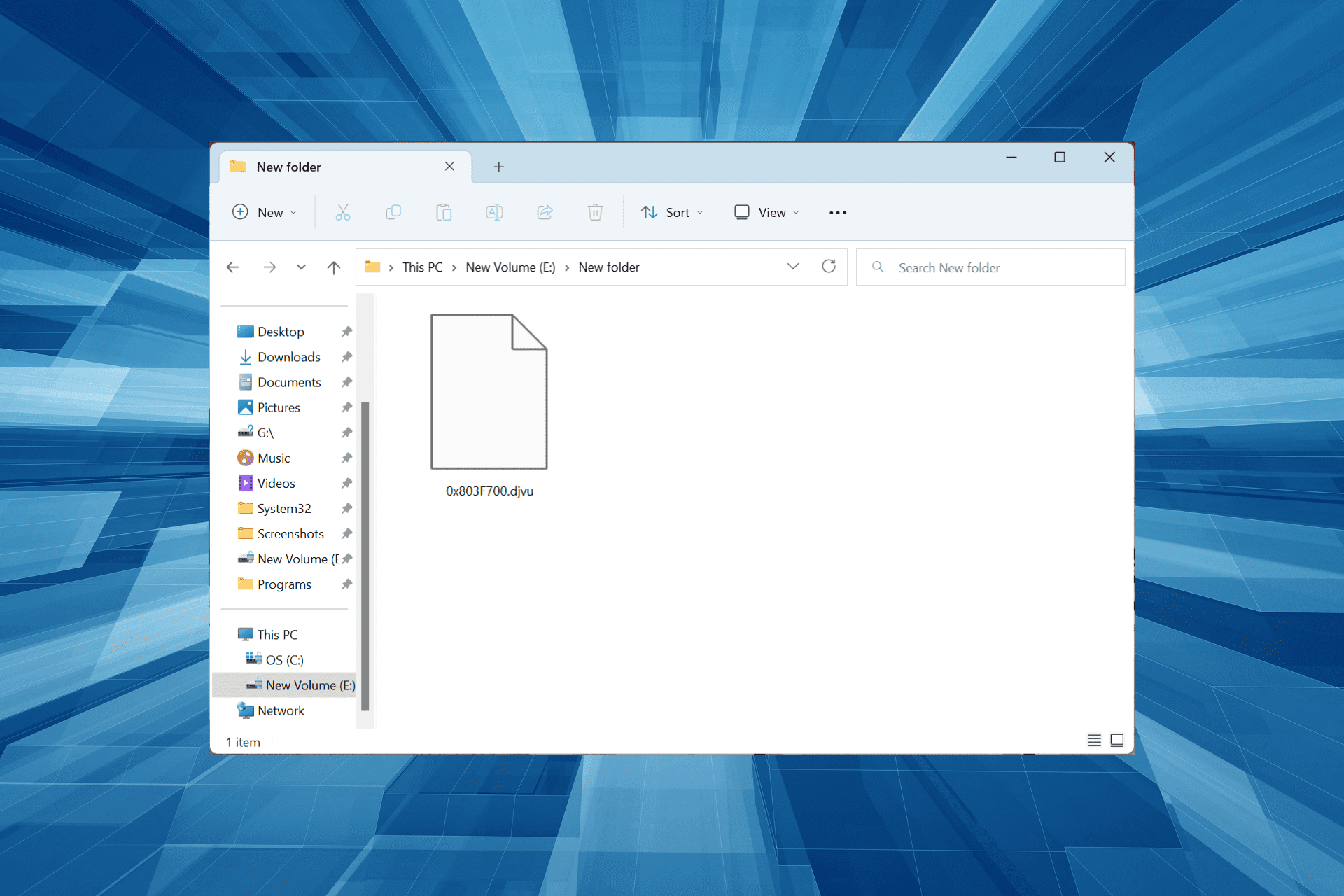
What Is the .djvu File Extension Virus and How to Remove It